Table of Contents
Key Takeaways
- AWS says its managed AWS MCP Server is now generally available, giving AI agents and coding assistants authenticated access to AWS services through Model Context Protocol.
- The durable search angle is not “AWS launched another tool”; it is how teams should connect agents to cloud accounts without creating an over-permissioned automation path.
- Start with read-only or sandbox access, log every agent action, and separate production credentials before connecting AWS MCP Server to coding workflows.
AWS MCP Server is now generally available, and that matters for teams experimenting with AI coding agents, cloud automation, and internal developer platforms. The official AWS News Blog describes it as a managed remote Model Context Protocol server that can give agents and coding assistants secure, authenticated access to AWS services. In plain English: instead of wiring every tool to custom AWS scripts, teams can let an MCP-compatible assistant talk to AWS through a common server interface.
That is powerful, but it is also exactly the kind of integration that deserves a security checklist before anyone points it at production. Hubkub has already covered agent deployment workflows in Cloudflare Agents and enterprise AI infrastructure in OpenAI on AWS. AWS MCP Server fits the same cluster: AI agents are moving from demos into real cloud operations, and the safest teams will treat access design as the product, not an afterthought.
What did AWS announce?
AWS announced the general availability of the AWS MCP Server on the AWS News Blog. The announcement positions the service as part of the Agent Toolkit for AWS, alongside tools intended to help coding agents build with AWS more effectively. AWS says the server gives agents access to AWS services through authenticated requests and can surface documentation, API references, “What’s New” posts, and getting-started information for agent workflows.
The important change is that this is no longer framed only as a preview experiment. General availability usually means a vendor is ready for broader operational adoption, support expectations, and production-adjacent evaluation. For Hubkub readers, the practical question is: should your team connect an AI assistant to AWS now, and if so, what guardrails should come first?
Why does AWS MCP Server matter for AI coding agents?
MCP is becoming a common connector layer for AI tools. A coding agent can use MCP servers to inspect docs, query services, open tickets, read files, or perform workflow actions without every vendor building a one-off plugin. In the AWS case, the value is obvious: cloud apps depend on IAM, Lambda, S3, CloudWatch, ECS, EKS, Bedrock, databases, and deployment pipelines. A capable agent that understands those services can speed up debugging and implementation.
The tradeoff is also obvious. If an AI assistant can call cloud APIs, mistakes become more expensive. A bad prompt, confused context, or overly broad role could inspect sensitive resources, create infrastructure drift, expose logs, or change production settings. That does not mean teams should avoid the tool. It means AWS MCP Server should be evaluated like any other privileged automation layer.
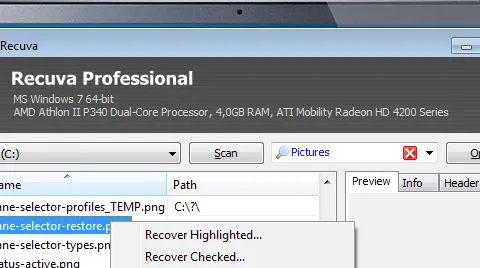
| Decision area | Safe default | Risk if skipped |
|---|---|---|
| Account scope | Start in a sandbox or non-production AWS account | Agent mistakes can touch live workloads |
| IAM permissions | Use least privilege and task-specific roles | One assistant session may gain broad cloud access |
| Logging | Keep CloudTrail and tool logs enabled | Teams cannot reconstruct what an agent did |
| Human approval | Require review for write/destructive actions | Automated changes can bypass normal change control |
How should teams pilot AWS MCP Server safely?
The safest first pilot is boring by design. Connect a coding assistant to documentation and read-only account discovery before allowing write actions. Ask it to explain deployed resources, draft Terraform changes, summarize CloudWatch errors, or locate the right AWS API reference. Do not begin by letting it modify IAM policies, rotate production resources, or deploy infrastructure without a human review step.
A practical rollout sequence looks like this:
- Create a dedicated test account or sandbox project for MCP evaluation.
- Use a named IAM role for the agent path, not a shared human admin credential.
- Allow read-only discovery first; add write permissions only for narrow, repeatable tasks.
- Keep CloudTrail, deployment logs, and CI logs tied to the agent workflow.
- Document which MCP client, assistant, account, and role are approved for use.
If the pilot is successful, move one workflow at a time into staging. Good candidates are documentation lookup, infrastructure explanation, cost-anomaly investigation, and drafting configuration changes. Riskier candidates include IAM edits, database changes, public network exposure, and production deployment. Those should stay behind human approval until the team has enough evidence.
Who should care first?
Platform teams, DevOps leads, cloud security engineers, and senior developers should care before general business users do. AWS MCP Server is most useful where developers already work with AWS daily and where the organization has enough cloud discipline to control roles, logs, and environments. It is less useful for teams that do not yet have clean IAM boundaries or a repeatable deployment process.
For readers building an AI-assisted workflow, this launch also connects to Hubkub’s broader Dev / IT Ops guide and AI guide. The winning pattern is not “give the model everything.” It is “give the agent the smallest useful window into the system, then expand only after logs prove the workflow is safe.”
What should you do now?
If your team is already testing AI coding tools, put AWS MCP Server on the evaluation list. Start with the official AWS announcement and the AWS Labs MCP documentation, then write down a small pilot policy before connecting credentials. The policy should answer four questions: which account can the agent access, which actions are allowed, who reviews changes, and where the audit trail lives.
The strongest near-term use case is not autonomous production control. It is guided acceleration: let the assistant read AWS context, explain errors, draft changes, and propose next steps while humans approve anything that can alter infrastructure. That balance gives teams the productivity benefit without turning a coding agent into an unsupervised cloud administrator.
FAQ
Q: What is AWS MCP Server?
A: AWS MCP Server is a managed remote Model Context Protocol server from AWS. It is designed to let AI agents and coding assistants access AWS services and AWS knowledge through an authenticated MCP interface.
Q: Is AWS MCP Server only for Amazon Q Developer?
A: AWS presents it as part of the broader Agent Toolkit for AWS, and the AWS Labs MCP project documents multiple MCP server options for AWS workflows. Teams should still verify which MCP clients and assistants are officially supported before production use.
Q: Should I give an AI agent write access to AWS?
A: Not at the start. Begin with read-only or sandbox access, then add narrow write permissions only after logging, approval, and rollback paths are working. IAM changes and production deployments should require human review.
Q: What is the biggest risk?
A: The biggest risk is over-permissioned agent access. A helpful assistant can become dangerous if it has broad cloud credentials, unclear approval rules, or no audit trail for the actions it performs.
Sources: AWS News Blog announcement; AWS Labs MCP documentation; AWS Labs MCP GitHub repository.